Latest Solutions Continuously Manage Risk to Mitigate Cyber-Physical Attacks, Loss of Networked Operations, Security Breaches, Insider Threats, and More
Vector Flow is demonstrating its powerful range of automation solutions at ISC West 2023, March 29-31 in Las Vegas.
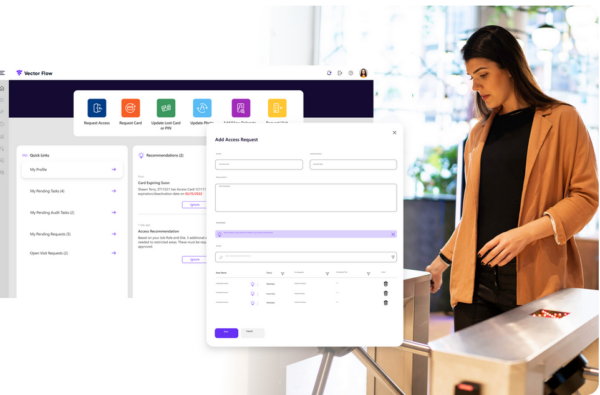
Most notably, Vector Flow is highlighting the new science of Physical Identity Access Management (PIAM) automation wherein organizations can autonomously manage individual identities over the entirety of their lifecycle under one platform.
“PIAM is the new security imperative for CSOs as they face new and emerging cyber-physical security threats and workforce management challenges,” said Ajay Jain, Founder and CEO of Vector Flow.
“Our ground-breaking PIAM automation platform effectively aggregates all the data related to identities, credentials, and permissions to provide organizations with data-driven insights and actionable intelligence. With such intelligence, organizations are empowered to better protect their people, property and assets with higher levels of cost- and operational-efficiencies.”
Physical Workforce Identity Suite
Vector Flow’s Physical Workforce Identity Suite delivers the new science of PIAM automation, providing insight-rich applications for automating all aspects of an identity lifecycle as it relates to the physical security domain. Designed to deliver a one-credential, one-identity solution across the enterprise, this powerful solution leverages advanced Artificial Intelligence (AI) technology to automate all identity management tasks such as on/off boarding of an Identity into physical security infrastructure, badging and credentialing, physical access management, access audits and compliance etc. The AI-enabled software uses learning algorithms to quickly identify and address security gaps and also delivers recommendations for security improvements and user tasks.
A new module recently added to the Physical Workforce Identity Suite is Vector Flow’s Workspace Occupancy application, which enables organizations to effectively track and forecast occupancy by departments, business units, personnel types, peak occupancy, day of the week, and more. The applications intuitive dashboard provides users with actionable insights that can be leveraged to identify popular and underutilized spaces and forecast future use of valuable space.
Vector Flow’s Workforce Identity Suite also now includes Next-Generation Visitor Management System (VMS) For Enterprises; a comprehensive solution with an easy-to-use application that provides organizations with the capability to manage visitors with provisions for touchless and secure check-in, watch list verifications, badge printing, health screenings, notifications, and more.
In addition to its Physical Workforce Identity Suite, Vector Flow is also demonstrating its other categories of solutions, Security Operations Center (SOC) Automation and Physical Security Threat Intelligence, at ISC West 2023.
SOC Automation Suite
Acts as a security nerve center, turning raw security data into insights and actions. The application drives actionable intelligence from a customer’s historical and daily physical security data. The solution features three AI-driven modules: SOC Alarm Reduction Manager, SOC Governance Manager, and SOC Predictive Maintenance Manager. The modules tie physical security processes together and automate time-consuming, manual tasks effectively increasing the overall productivity of SOC operators/agents, while maintaining compliance through data-generated reports, and decreasing downtime of connected devices and associated maintenance costs.
Physical Security Threat Intelligence
Comprises of applications whereby the data is collected and processed from security logs, journals, transaction data to understand who the threat actors are and what are the compromised areas in the physical security infrastructure. Using advanced AI and Machine Learning algorithms, the solution uncovers security vulnerabilities and makes risk mitigation recommendations to identify and address operational and security gaps, deliver recommendations for improvements, and make hidden details of an enterprise’s physical security operational state visible.
visit: vectorflow.com
See more articles on: Vector
Source: vectorflow.com
